LTI™ Security Update
Version 1.0
| Date Issued: | 22 July 2019 |
| Status: | This document is made available for adoption by the public community at large. |
| This version: | https://www.imsglobal.org/spec/lti/security-update/v1p0/ |
IPR and Distribution Notices
Recipients of this document are requested to submit, with their comments, notification of any relevant patent claims or other intellectual property rights of which they may be aware that might be infringed by any implementation of the specification set forth in this document, and to provide supporting documentation.
1EdTech takes no position regarding the validity or scope of any intellectual property or other rights that might be claimed to pertain to the implementation or use of the technology described in this document or the extent to which any license under such rights might or might not be available; neither does it represent that it has made any effort to identify any such rights. Information on 1EdTech's procedures with respect to rights in 1EdTech specifications can be found at the 1EdTech Intellectual Property Rights web page: http://www.imsglobal.org/ipr/imsipr_policyFinal.pdf.
Copyright © 2019 1EdTech Consortium. All Rights Reserved.
Use of this specification to develop products or services is governed by the license with 1EdTech found on the 1EdTech website: http://www.imsglobal.org/speclicense.html.
Permission is granted to all parties to use excerpts from this document as needed in producing requests for proposals.
The limited permissions granted above are perpetual and will not be revoked by 1EdTech or its successors or assigns.
THIS SPECIFICATION IS BEING OFFERED WITHOUT ANY WARRANTY WHATSOEVER, AND IN PARTICULAR, ANY WARRANTY OF NONINFRINGEMENT IS EXPRESSLY DISCLAIMED. ANY USE OF THIS SPECIFICATION SHALL BE MADE ENTIRELY AT THE IMPLEMENTER'S OWN RISK, AND NEITHER THE CONSORTIUM, NOR ANY OF ITS MEMBERS OR SUBMITTERS, SHALL HAVE ANY LIABILITY WHATSOEVER TO ANY IMPLEMENTER OR THIRD PARTY FOR ANY DAMAGES OF ANY NATURE WHATSOEVER, DIRECTLY OR INDIRECTLY, ARISING FROM THE USE OF THIS SPECIFICATION.
Public contributions, comments and questions can be posted here: http://www.imsglobal.org/forums/ims-glc-public-forums-and-resources.
© 2019 1EdTech Consortium, Inc. All Rights Reserved.
Trademark information: http://www.imsglobal.org/copyright.html
Abstract
This document provides a security update to address cross-site request forgery threats applicable to versions of LTI released prior to v1.3. The security updates described here apply specifically to LTI v1.0 and v1.1.1. This solution may also be applied to other versions of LTI (1.2 and 2.0) but are not directly addressed here as 1EdTech encourages implementors to adopt the latest version (1.3) as soon as possible.
LTI Security Update: LTI Launch with Authentication Flow Representing New Security Requirements for LTI v1.0.1 and LTI v1.1.2
1. Introduction
The purpose of this document is to address a login cross-site request forgery (CSRF) threat that has been identified to 1EdTech.
1.1 Documentation
The following LTI v1.3 and LTI Advantage related specification documents are available:
- 1EdTech Security Framework Version 1.0 [SEC-10] specification
- LTI Core Version 1.3 [LTI-13] specification
- Deep Linking Version 2.0 [LTI-DL-20] specification
- Names and Role Provisioning Services Version 2.0 [LTI-NRPS-20] specification
- Assignment and Grade Services Version 2.0 [LTI-AGS-20] specification
- LTI Advantage Implementation Guide [LTI-IMPL-13] specification
This security update, already accounted for in the LTI Advantage specifications, applies specifically to these earlier versions of LTI:
1.2 Conformance Certification Options
- Conformance certification testing for this security update as LTI v1.0.1 and v1.1.2 is available to 1EdTech members.
2. LTI 1.1.2 Launch Flow Overview
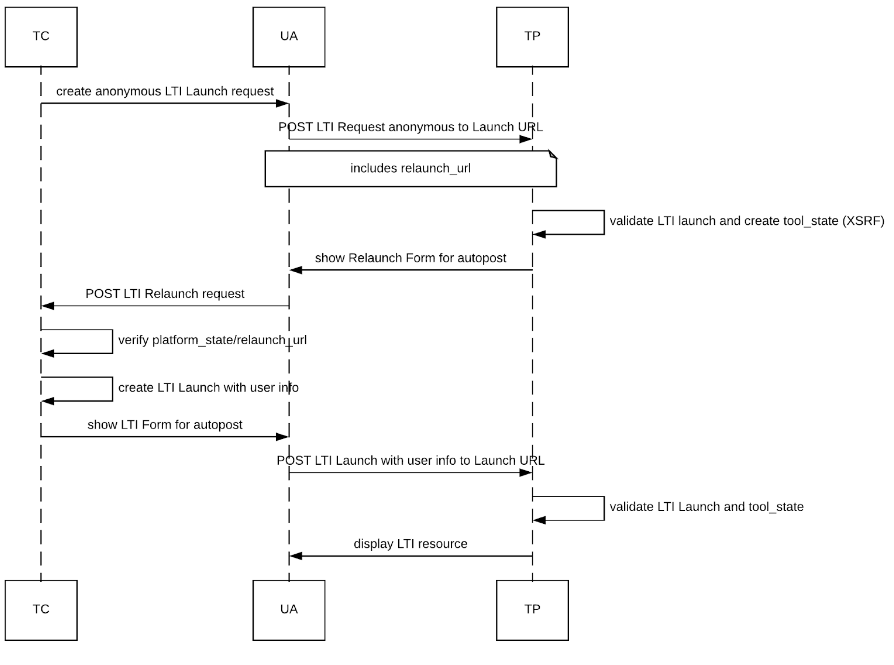
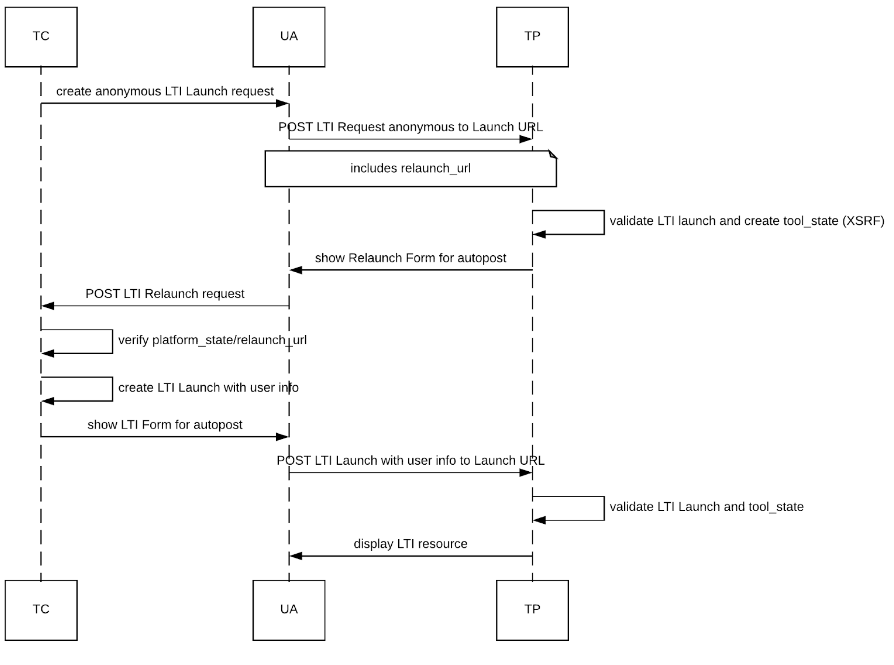
In this flow, each LTI message request is treated as an authentication request, which triggers an implicit flow between the Tool Provider (TP) and the Tool Consumer (TC).
Identity information will only be sent to a TP once an XSRF token has been exchanged (see tool_state). The initial launch is therefore anonymous, and must not contain any user identity information, including user_id. It contains the relaunch_url which will allow the TP to pass the token (tool_state) back to the TC to re-initiate a full launch, now containing user identity.
The first stage of the launch will always be made anonymously, and will carry extra parameters to let a TP complete the workflow to find out which user the LTI launch is for.
The following stages of the workflow permit the TP to handshake with the TC to agree on who the user is. This results in a full, user-included, LTI launch payload being sent to the TP.
4. Implementation Guidelines
4.1 Use State to Pass Information in the Flow
This avoids for example to have to store additional state into the tool application state by including, in addition to a proper XSRF token, additional data for processing the request when the authentication response is received. For example, the state (TP or TC) can be a signed or encrypted JWT.
Annex Other documents where this was discussed and led to this proposal:
Original issue reported: https://github.com/IMSGlobal/security-framework/issues/52
A. References
A.1 Informative references
- [BLTI-10]
- 1EdTech Basic Learning Tools Interoperability v1.0. C. Severance. 1EdTech Consortium. May 2010. 1EdTech Final Release. URL: https://www.imsglobal.org/lti/
- [LTI-11]
- 1EdTech Learning Tools Interoperability (LTI)® Implementation Guide. G. McFall; M. McKell; L. Neumann; C. Severance. 1EdTech Consortium. March 13, 2012. URL: https://www.imsglobal.org/specs/ltiv1p1
- [LTI-13]
- 1EdTech Learning Tools Interoperability (LTI)® Core Specification v1.3. C. Vervoort; N. Mills. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/lti/v1p3/
- [LTI-AGS-20]
- 1EdTech Learning Tools Interoperability (LTI)® Assignment and Grade Services. C. Vervoort; E. Preston; M. McKell; J. Rissler. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/lti-ags/v2p0/
- [LTI-DL-20]
- 1EdTech Learning Tools Interoperability (LTI)® Deep Linking 2.0. C. Vervoort; E. Preston. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/lti-dl/v2p0/
- [LTI-IMPL-13]
- 1EdTech Learning Tools Interoperability® Advantage Implementation Guide. C. Vervoort; J. Rissler; M. McKell. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/lti/v1p3/impl/
- [LTI-NRPS-20]
- 1EdTech Learning Tools Interoperability (LTI)® Names and Role Provisioning Services. C. Vervoort; E. Preston; J. Rissler. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/lti-nrps/v2p0/
- [SEC-10]
- 1EdTech Security Framework v1.0. C. Smythe; C. Vervoort; M. McKell; N. Mills. 1EdTech Consortium. April 2019. 1EdTech Final Release. URL: https://www.imsglobal.org/spec/security/v1p0/